North Korea’s Lazarus Group created a blockchain game to exploit a vulnerability in Google’s Chrome browser, install spyware and steal crypto wallet credentials, along with other user data.
In an Oct. 23 report, cybersecurity firm Kaspersky Labs analysts Vasily Berdnikovand and Boris Larin said they found the Lazarus Group exploit in May and reported it to Google, which has since fixed the issue.
According to Berdnikov and Larin, hackers in the Lazarus Group used the game to coax users to a malicious website and infect computers with its malware Manuscript, which it has been using since at least 2013.
The code allowed the hackers to corrupt Chrome’s memory, eventually giving them access to users’ cookies, authentication tokens, saved passwords, and browsing history—everything they needed to steal user funds.

Another issue with the Javascript security mechanism V8 sandbox allowed Lazarus to access PCs to investigate whether continuing a cyber attack was worthwhile.
“We were able to extract the first stage of the attack — an exploit that performs remote code execution in the Google Chrome process,” Berdnikov and Larin said.
“After confirming that the exploit was based on a zero-day vulnerability targeting the latest version of Google Chrome, we reported our findings to Google the same day.”
Two days after Google became aware of the exploit, it released an updated patch to solve the issue.
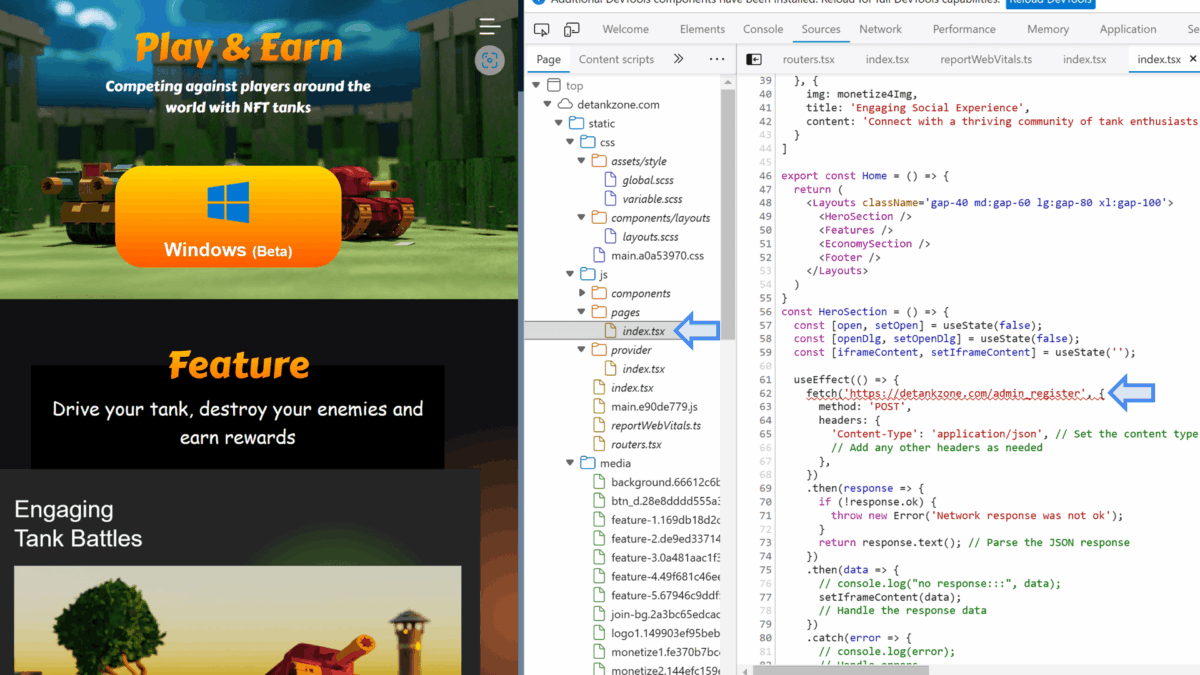
Stolen source code used to create game
The game itself, DeTankZone or DeTankWar, was a fully playable play-to-earn multiplayer online battle arena game with non-fungible tokens (NFT) tanks. Players could battle each other in online competition.
Berdnikov and Larin said Lazarus stole the source code from another legitimate game and promoted the pirated version heavily on social media.
The fake game had a website and promotional images generated using artificial intelligence.

“On the surface, this website resembled a professionally designed product page for a decentralized finance (DeFi) NFT-based (non-fungible token) multiplayer online battle arena (MOBA) tank game, inviting users to download a trial version,” Berdnikov and Larin said.
“But that was just a disguise. Under the hood, this website had a hidden script that ran in the user’s Google Chrome browser, launching a zero-day exploit and giving the attackers complete control over the victim’s PC.”
Microsoft Security also flagged the game in a May post on X, noting that the malicious game DeTankWar was delivering new custom ransomware that Microsoft dubbed FakePenny.
“Microsoft has identified a new North Korean threat actor, Moonstone Sleet (Storm-1789), that combines many tried-and-true techniques used by other North Korean threat actors with unique attack methodologies for financial and cyberespionage objectives,” Microsoft Security said.
“Moonstone Sleet is observed to set up fake companies and job opportunities to engage with potential targets, employ trojanized versions of legitimate tools, create a malicious game called DeTankWar, and deliver a new custom ransomware that Microsoft has named FakePenny.”
Losses to Lazarus Group estimated to be over $3 billion
Lazarus has become arguably the most notorious crypto hacker group since coming onto the scene in 2009. United States cybersecurity firm Recorded Future estimated in 2023 that North Korean hackers stole over $3 billion in crypto in the six years leading up to 2023.
A United Nations report also found North Korean hackers stole a significant amount of crypto assets in 2022, with estimates between $630 million and more than $1 billion, after groups started targeting networks of foreign aerospace and defense companies.
Blockchain detective ZachXBT estimates Lazarus laundered over $200 million in crypto from 25 hacks between 2020 and 2023. In an Aug. 15 post on X, he also claimed to have uncovered evidence of a sophisticated network of North Korean developers earning $500,000 a month working for “established” crypto projects.
At the same time, the US Treasury Department has also accused Lazarus of being the main culprit behind the 2022 attack on Ronin Bridge, which netted the hackers over $600 million in crypto.